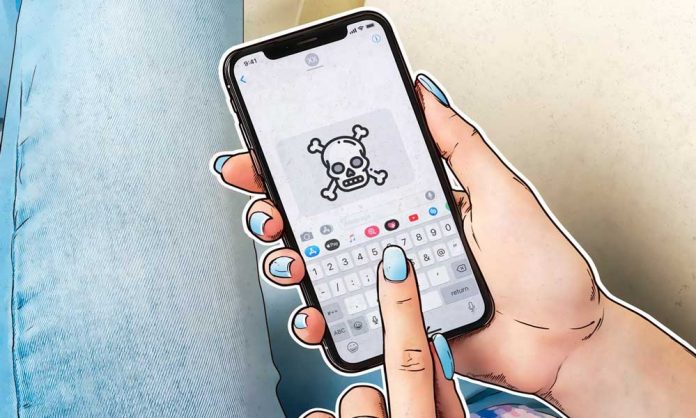
A vulnerability in the iOS operating system has permanently broken the protection of hundreds of millions of iPhones, security researchers have discovered, adding that Apple is unable to close the vulnerability with any software update.
An IT expert who calls himself “axi0mX” on Twitter described his vulnerability in all devices that use the system “iOS” with A5 to A11 processors, including all smartphones, from “iPhone S4” to”iPhone X “. Tablet PCs, Apple watches, and even their TV could be at risk.
iPhone 11 vs Galaxy Note 10+ vs Mate30 Pro Battery Comparison
The user, who writes on his account that he is an expert in the service of “Get Hub” on the Internet, the flaw of these phones and explained the weaknesses in the operating system. But the real danger, according to the expert, is that “Apple” can not close this gap with any update to the system.
The expert called “Get Hop” this vulnerability security checkm8, adding that it is located in the root of the system and gives attackers deep access to devices running the system “iOS” to a level with which it is impossible to prevent “Apple” Or fix it in a future software update, which could make it one of the most serious loopholes in iPhone for years.
EPIC JAILBREAK: Introducing checkm8 (read “checkmate”), a permanent unpatchable bootrom exploit for hundreds of millions of iOS devices.
Most generations of iPhones and iPads are vulnerable: from iPhone 4S (A5 chip) to iPhone 8 and iPhone X (A11 chip). https://t.co/dQJtXb78sG
— axi0mX (@axi0mX) September 27, 2019
However, Apple seems to have fixed this vulnerability in its processor (A12), which means that the phones “iPhone 10 S” and “iPhone 10 XR” and “iPhone 11” and “iPhone 11 Pro” out of danger.
This loophole can install non-Apple software on the phone. This may be a pleasure for users of these phones, but there is a lot of malware as well. In order to break the protection of “Apple” phones and “iPad”, hackers must connect the phone to their devices through the port “USB”, and must be activated each time through a computer. But it is not possible to break the protection remotely and install programs.
But what does this security gap mean for users? “This is probably the greatest development in the community to break the protection of iOS (jailbreak),” says a Twitter user.
The security vulnerability is that this vulnerability can exceed the so-called read-only memory (ROM) in the device, which is the memory used when the device is first connected and determines in the “Apple” operating system, programs and applications that run on the device. Apple has yet to comment on the discovery.